Apr242013
Resolve "Access is Denied" using PSExec with a Local Admin Account
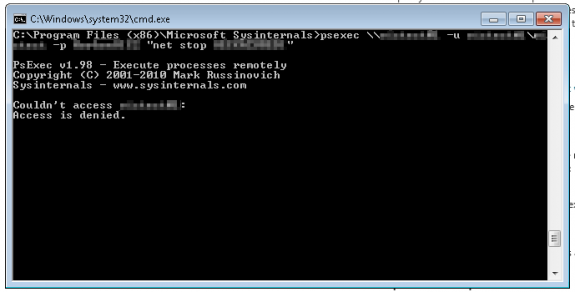
Upon trying to enable remote command execution using PSExec, I ran into an issue trying to login with a local administrator account on my remote server: Access is denied.
Apparently, if you have an account that's a local Administrator, Remote UAC will block them from being able to do things like remote execution.
A quick way to test if this might be your issue:
- Access the server via filesharing (\\YOURSERVER\C\$); you should be able to login with your credentials.
- Access the server via filesharing, but this time go to the admin share (\\YOURSERVERNAME\ADMIN\$); this should fail. This is what we need to fix.
To get around this, you can make a registry change:
- Open RegEdit on your remote server
- Navigate to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System
- Add a new DWORD value called LocalAccountTokenFilterPolicy
- Set its value to 1
- Reboot your remove server
- Try running PSExec again from your local server
You should be able to execute remote commands.
Solution found via Admin Arsenal Support: Can't access the ADMIN\$ using a local user account.